Categories: General Information
What is Zero-Knowledge Proof? Enhancing Privacy and Security
What is Zero-Knowledge Proof? Discover how these cryptographic protocols enable verification without revealing sensitive information. Gain insights into their applications and understand the potential of Zero-Knowledge Proof in safeguarding digital interactions.
In the digital age where privacy and security are of utmost importance, zero-knowledge proofs have emerged as a groundbreaking cryptographic concept. What is Zero-Knowledge Proof? This blog aims to provide a comprehensive understanding of zero-knowledge proofs, their significance, functioning, and practical applications. We will also explore the limitations and drawbacks associated with this powerful privacy-enhancing technology.
Table of Contents
What is zero-knowledge proof?
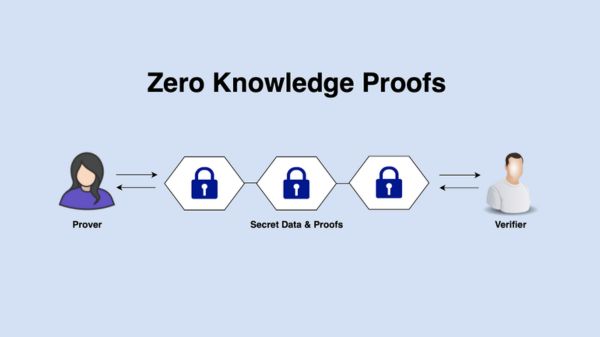
What is Zero-Knowledge Proof? Zero-knowledge proof (ZKP) is a cryptographic protocol that enables one party, known as the prover, to convince another party, the verifier, that a specific statement or fact is true without revealing any additional information apart from the statement's validity. In essence, a zero-knowledge proof allows the prover to demonstrate knowledge of certain data or credentials without exposing the actual data itself.

Why do we need zero-knowledge proofs?
Zero-knowledge proofs play a pivotal role in enhancing privacy, confidentiality, and security in various scenarios. They address the challenge of validating information without disclosing sensitive data, thereby enabling trust and reducing the need for blind reliance on third parties. Zero-knowledge proofs provide a powerful tool to establish authenticity, verify identities, and perform secure computations without compromising data privacy.
How do zero-knowledge proofs work?
Zero-knowledge proofs employ complex mathematical algorithms to construct a protocol that enables the prover to convince the verifier of the statement's truthfulness without revealing the underlying information. This is achieved through a series of interactions between the prover and the verifier, where the prover demonstrates knowledge of the statement in a way that convinces the verifier without disclosing any additional details.
The underlying cryptographic techniques utilized in zero-knowledge proofs include concepts such as commitment schemes, challenge-response protocols, and interactive proofs. These techniques allow the prover to provide evidence of the statement's validity while preserving the confidentiality of sensitive data.
Use-cases for zero-knowledge proofs
a. Authentication and Identity Verification: Zero-knowledge proofs can be employed to verify identities and authenticate users without exposing sensitive personal information. This can be particularly useful in scenarios such as access control, password authentication, or digital identity systems.
b. Confidential Transactions: Zero-knowledge proofs have found application in privacy-focused cryptocurrencies, enabling the verification of transaction validity without disclosing transaction details, including sender, recipient, and transaction amount. This ensures financial privacy while maintaining transparency.
c. Secure Data Sharing and Outsourced Computation: Zero-knowledge proofs allow data owners to prove the correctness of computations performed on their data without revealing the actual data. This enables secure outsourcing of computation tasks and collaborative data analysis while protecting data privacy.
d. Audit and Compliance: Zero-knowledge proofs can be utilized to verify compliance with regulations or prove adherence to specific criteria without disclosing sensitive business information. This can streamline audits and compliance processes while safeguarding confidentiality.
Drawbacks of using zero-knowledge proofs
a. Computational Overhead: Zero-knowledge proofs can involve complex mathematical computations, resulting in higher computational requirements and increased processing time. This can limit the scalability and efficiency of systems employing zero-knowledge proofs.
b. Setup and Trust Assumptions: Some zero-knowledge proof systems require initial setup and trusted parameters, which may introduce vulnerabilities if not implemented carefully. The reliance on trusted setups can undermine the trustless nature of certain applications.
c. Complexity and Development Challenges: Designing and implementing zero-knowledge proof protocols can be intricate and require specialized expertise. Ensuring the correctness and security of such protocols can pose challenges during development and may limit their widespread adoption.
Future of Zero-Knowledge Proof
The future of Zero-Knowledge Proofs (ZKPs) is promising and holds significant potential for various fields, especially in the context of blockchain technology and privacy-enhancing applications. ZKPs are cryptographic protocols that enable one party (the prover) to prove the validity of a statement to another party (the verifier) without revealing any information about the underlying data used to generate the proof.
Here are some potential future developments and applications of Zero-Knowledge Proofs:
- Privacy and Confidentiality: ZKPs can continue to play a critical role in enhancing privacy and confidentiality in various domains. In blockchain systems, ZKPs can enable private transactions and confidential smart contracts, ensuring that sensitive data remains hidden from unauthorized parties.
- Scalability and Efficiency: ZKPs have the potential to improve the scalability and efficiency of blockchain networks. By reducing the amount of data needed to be processed and validated on-chain, ZKPs can alleviate the scalability challenges faced by many blockchain platforms.
- Interoperability: ZKPs can facilitate interoperability between different blockchain networks by enabling secure and trustless cross-chain transactions and data sharing without revealing sensitive information.
- Decentralized Identity (DID): ZKPs can be utilized in decentralized identity solutions, allowing users to prove specific attributes about themselves without disclosing unnecessary personal information. This can enhance user privacy and reduce reliance on centralized identity providers.
- Auditability and Compliance: In financial systems, ZKPs can enable verifiable and auditable transactions without exposing sensitive financial information, making compliance with regulatory requirements more feasible.
- Secure Voting: ZKPs can enhance the security and privacy of voting systems by enabling voters to prove the validity of their votes without disclosing their voting preferences.
- Supply Chain and IoT: ZKPs can be applied in supply chain management and the Internet of Things (IoT) domain to ensure data integrity, provenance, and authenticity without revealing sensitive business information.
- Post-Quantum Cryptography: ZKPs could potentially play a role in post-quantum cryptographic schemes, providing robust security even against quantum computing attacks.
Despite the potential benefits, there are still challenges to overcome in the widespread adoption of Zero-Knowledge Proofs. These challenges include computational complexity, the need for trusted setups in some ZKP constructions, and the necessity for thorough security audits to ensure protocol soundness.
As research and development in cryptography and blockchain technology continue to progress, we can expect further advancements and innovations in Zero-Knowledge Proofs, making them more practical, efficient, and versatile for a wide range of applications. Their ability to strike a balance between privacy and transparency is likely to be a critical factor in shaping the future of digital ecosystems, especially in the context of data protection and secure communication.
Conclusion
What is Zero-Knowledge Proof? Zero-knowledge proofs offer a remarkable cryptographic solution that enhances privacy, security, and trust in a variety of domains. By allowing verifiable statements without exposing sensitive information, zero-knowledge proofs pave the way for confidential transactions, secure data sharing, and identity verification. However, it is crucial to navigate the potential drawbacks and address the computational overhead and trust assumptions associated with their implementation. As technology continues to advance, zero-knowledge proofs hold immense potential to reshape the digital landscape, empowering individuals and organizations with enhanced privacy and security capabilities. Follow https://uniultra.xyz/ for more blockchain updates.
